stuxnet virus removal tool instructions
how the STUXNET VIRUS SPREADS VIA USB STICKS .. Dangerous Flash Drives
And here it comes again. You thoughT, that turning the "auto-run" feature for removable drives off is sufficient and no "Worm/Autorun" can harm you again. And I bet you are pretty sure about it. I'm sorry, you are wrong.
Few days ago, a very strange sample appeared here in our lab. In fact, it was so interesting, it deserved these lines. At the moment, both samples – two drivers which use the rootkit technology for hiding themselves – are detected by AVG. These are quite "standard" rootkits, except, one of them is signed with valid certificate of Realtek Semicondutor Corp. In fact, the certificate is not valid right now, but it _was_ and that's a bit scary as this could confuse a lot of antivirus products. Valid certificate is still kind of "quality mark".
But while this is very unusual, the biggest surprise is the method of distribution. This malware uses completely new technique and, unfortunately, still opened vulnerability in MS Windows where the main role plays the ".lnk" file – yes, the well known Windows Shortcut File. In this particular case, following files are placed on the infected USB Flash Drive:
Do you have Total Commander, or Windows Explorer? Or any other file manager which supports icons? You've got a problem – of course, only in case you plug in the infected flash drive and open it with one of those file managers. The process of infection starts immediately, two files are dropped to your computer:
%system%\Drivers\mrxcls.sys
%system%\Drivers\mrxnet.sys
Two services are created to start them:
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\MRxCls]
"Description"="MRXCLS"
"DisplayName"="MRXCLS"
"Group"="Network"
"ImagePath"="\\??\\C:\\WINDOWS\\system32\\Drivers\\mrxcls.sys"
"Start"=dword:00000001
"Type"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\MRxNet]
"Description"="MRXNET"
"DisplayName"="MRXNET"
"Group"="Network"
"ImagePath"="\\??\\C:\\WINDOWS\\system32\\Drivers\\mrxnet.sys"
"Start"=dword:00000001
"Type"=dword:00000001
Finally, all the malware files (.lnk and .tmp) are hidden, so the victim probably won't even notice there are some other files on the flash drive.
After this, common rootkit behavior follows including "process injection", "API hooking", etc.. The driver injects the malware code into following processes:"
lsass.exe
svchost.exe
services.exe
Maybe, this is the only single threat that uses this vulnerability, but we can probably expect many others – until the vulnerability is closed. Microsoft knows about it and, hopefully, they'll do something about it soon. Until that time, you should, once again, care about your Flash Drives and the source they came from (remember the good old times with all the infected floppy disc?). And, of course, you should stay protected..
Thanks to Peter Gramantik and Arek Kupka
http://greatis.com/security/stuxnet_remover.html
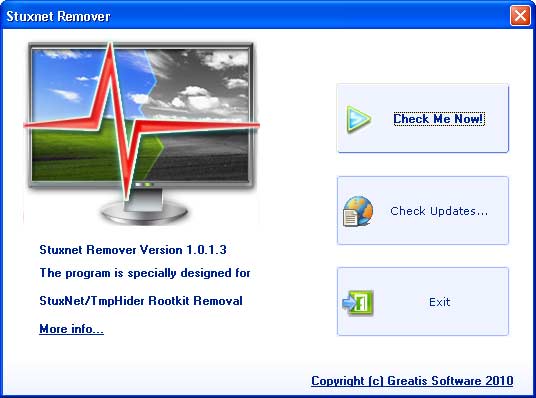
How Stuxnet Remover works?
Stuxnet Remover is able to detect and remove the active infecton.It can find the Rootkit drivers and other files made by Stuxnet Rootkit.
- C:\WINDOWS\system32\drivers\mrxcls.sys
- C:\WINDOWS\system32\drivers\mrxnet.sys
- C:\WINDOWS\inf\mdmcpq3.PNF
- C:\WINDOWS\inf\mdmeric3.PNF
- C:\WINDOWS\inf\oem6C.PNF
- C:\WINDOWS\inf\oem7A.PNF
In addition the Stuxnet Remover is able to detect and remove malicious "lnk" and "tmp" files stored on the removable media.
- ~WTR4132.tmp
- "Copy of Copy of Copy of Copy of Shortcut to.lnk"
- "Copy of Copy of Copy of Shortcut to.lnk"
- "Copy of Copy of Shortcut to.lnk"
- "Copy of Shortcut to.lnk"
- ~WTR4141.tmp
KB2347290
kb2286198 << still
Stuxnet Virus, or also known as Winsta, devouring all the vacant land on the hard disk until full. According to Alfons Tanujaya, antivirus analysts from Vaksincom, to detikINET, Friday (07/30/2010), Indonesia is the country with the second largest Stuxnet victims in the world after Iran.
The virus initially spread from various adult sites, pirated programs and content 'gray' other was quite disturbing. Here are the steps to eradicate the virus, as manifested by antivirus analysts Vaksincom Adi Saputra:
1. Using Dr. Web CureIt
Adi suggested that the victim Winsta Stuxnet alias to download a virus removal software. Removal Tools called Dr.Web CureIt can be downloaded from the site FreeDrWeb.com
2. Registry Fix
Then, Adi registry suggest improvements in Windows that has been modified by a virus. How, first of all, copy the script below into WordPad file.
[Version]
Signature="$Chicago$"
Provider=Vaksincom Oyee
[DefaultInstall]
AddReg=UnhookRegKey
DelReg=del
[UnhookRegKey]
HKCU, Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced, ShowSuperHidden,0x00010001,1
HKCU, Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced, SuperHidden,0x00010001,1
HKCU, Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced, HideFileExt,0x00010001,0
HKLM, SOFTWARE\CLASSES\batfile\shell\open\command,,,"""%1"" %*"
HKLM, SOFTWARE\CLASSES\comfile\shell\open\command,,,"""%1"" %*"
HKLM, SOFTWARE\CLASSES\exefile\shell\open\command,,,"""%1"" %*"
HKLM, SOFTWARE\CLASSES\piffile\shell\open\command,,,"""%1"" %*"
HKLM, SOFTWARE\CLASSES\regfile\shell\open\command,,,"regedit.exe "%1""
HKLM, SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon, Shell,0, "Explorer.exe"
[del]
HKLM, SYSTEM\CurrentControlSet\Services\MRxCls
HKLM, SYSTEM\CurrentControlSet\Services\MRxNet
HKLM, SYSTEM\ControlSet001\Services\MRxCls
HKLM, SYSTEM\ControlSet002\Services\MRxNet
HKLM, SYSTEM\CurrentControlSet\Services\Enum\Root\LEGACY_MRXClS
HKLM, SYSTEM\CurrentControlSet\Services\Enum\Root\LEGACY_MRXNET
HKLM, SYSTEM\ControlSet001\Services\Enum\Root\LEGACY_MRXClS
HKLM, SYSTEM\ControlSet002\Services\Enum\Root\LEGACY_MRXNET
Then, save the file with the name 'repair.inf'. Use the Save as type option to Text Document in order to avoid mistakes. Then, right click the file 'repair.inf', select 'Install' and restart the computer.
"Clean up temporary files, this in order to prevent the rest of the trojan is trying to become active again. Use tools such as ATF Cleaner or use the features of Windows that is the Disk Clean-Up," wrote Adi.
3. Emergency Solutions
In addition, the following is a script that can be used in emergencies to prevent re-infecting Winsta not. Save the following script with the name Winsta.bat (file type: Text)
@echo off
del /f c:\windows\system32\winsta.exe
rem rd c:\windows\system32\winsta.exe
md c:\windows\system32\winsta.exe
del /f c:\windows\system32\drivers\mrxnet.sys
rem rd c:\windows\system32\drivers\mrxnet.sys
md c:\windows\system32\drivers\mrxnet.sys
del /f c:\windows\system32\drivers\mrxcls.sys
rem rd c:\windows\system32\drivers\mrxcls.sys
md c:\windows\system32\drivers\mrxcls.sys
attrib +r +h +s c:\windows\system32\winsta.exe
attrib +r +h +s c:\windows\system32\drivers\mrxnet.sys
attrib +r +h +s c:\windows\system32\drivers\mrxnet.sys
Once completed, double-click the resulting file Winsta.bat. For optimal cleaning and prevent re-infection, re-use antivirus software that scans an updated and properly recognize this virus.
information from October 21, 2010:
Manufacturers of virus scan software have reported massive Stuxnet infections in some countries, with no distinction being made as to whether office PCs or industrial systems are affected. In none of the cases known to Siemens from the industrial environment was a plant's control system affected.
In the three months since Stuxnet appeared for the first time, a total of 19 Siemens customers worldwide from an industrial environment have reported an infection with the Trojan (as of October 21, 2010).
In all cases Stuxnet exploited security gaps in Windows-based operating systems. The virus could be removed in every case without any adverse effects on plant processes. In none of the cases did Stuxnet influence control software or even attempt to do so.
This behavior corresponds to the insights gained from the analysis that Siemens carried out on the virus. Stuxnet searches systematically for a very specific plant configuration. If it does not find such a configuration, the virus is not activated.
Product Information dated October 01, 2010:
- Latest news on the infected computers::
To date, we know of 15 systems infected worldwide. In all cases the malware could be removed. In none of these cases did the infection cause an adverse impact to the automation system. Since the end of August no new infections were registered.
Recommended procedure for detecting and removing "stuxnet" (updated August 04, 2010)
We recommend examining the following computer types:
- Embedded systems (e.g. Microbox)
- Other computers
- Infrastructure computers (file servers, domain controllers, other servers...)
- Computers with and without WinCC installed
- Virtual machines (e.g. VMWARE installations))
The individual activities should be carried out based on the following procedure:
Important note:
Product Information dated September 17, 2010:
Analysis of virus and status of investigations
- The virus has been isolated on a test system in order to carry out more extensive investigations. Previously analyzed properties and the behavior of the virus in the software environment of the test system suggest that we are not dealing with the random development of one hacker, but with the product of a team of experts who must have IT expertise as well as specific know-how about industrial controls, their deployment in industrial production processes and corresponding engineering knowledge.
- As far as we know at the moment, industrial controls from Siemens are affected. The Trojan is activated whenever WinCC or PCS7 software from Siemens is installed.
- Further investigations have shown that the virus can theoretically influence specific processes and operations in a very specific automation environment or plant configuration in addition to passing on data. This means that the malware is able, under certain boundary conditions, to influence the processing of operations in the control system . However, this behavior has not yet been verified in tests or in practice.
- The behavioral pattern of Stuxnet suggests that the virus is apparently only activated in plants with a specific configuration. It deliberately searches for a certain technical constellation with certain modules and certain program patterns which apply to a specific production process. This pattern can, for example, be localized by one specific data block and two code blocks.
- This means that Stuxnet is obviously targeting a specific process or a plant and not a particular brand or process technology and not the majority of industrial applications.
- This conclusion also coincides with the number of cases known to Siemens where the virus was detected but had not been activated, and could be removed without any damage being done up to now. · This kind of specific plant was not among the cases that we know about.
How is it possible to say whether an automation system corresponds to the specific program pattern and what counter-measures recommended are?
- The malware carries its own blocks (for example, DB890, FC1865,1874) and tries to load them into the CPU and integrate them into the program sequence. If the above-mentioned blocks are already present, the malware does not infiltrate the user program.
- If the above-mentioned blocks were not present in the original program and are now detected, the virus has infected the system. In this case Siemens urgently recommends restoring the plant control system to its original state.
Is the current Microsoft Patch compatible with SIMATIC Software
- The current Microsoft Patch KB2347290 was successfully tested with SIMATIC WinCC and SIMATIC PCS 7.
http://support.automation.siemens.com/WW/view/en/18490004
http://support.automation.siemens.com/WW/view/en/18752994
Product Information dated September 07, 2010:
- Latest news on the infected computers:
To date, we know of 15 systems infected worldwide. In none of these cases did the infection cause an adverse impact to the automation system.
Product Information dated August 24, 2010:
- Latest news on the infected computers:
To date, we know of 12 systems infected worldwide. In none of these cases did the infection cause an adverse impact to the automation system.
Product Information dated August 13, 2010:
- We continue to recommend to customers that they utilize the Siemens-approved virus scanner and make sure that they have sufficient IT security standards in place (e.g. network security, no active USB connections in the production environment, etc.). Operating systems must be checked continuously to ensure that they are up-to-date.
- To the best of our knowledge right now, the malware is active only when very specific project structures in the automation system are present..
- To date, we know of nine systems infected worldwide. In none of these cases did the infection cause an adverse impact to the automation system.
Product Information dated August 03, 2010:
- Important note on the Microsoft Patch
The Microsoft Patch only prevents that the trojan from being installed automatically on the system. If a user with admin-rights opens an infected LNK-file by mouse click on a computer on which the Microsoft Patch is installed, the computer will become infected - if no virus scanner has been installed. To avoid such an infection, it is strongly recommended that users only log in with power user rights. Power users do not have the necessary permissions to start code from another drive. For additional security use an approved virus scanner.
posted by u2r2h at Wednesday, October 27, 2010
 Earth's magnetic field:
Earth's magnetic field:

0 Comments:
Post a Comment
<< Home